Why you can trust Sunlight Media
- Expertise and Experience:Our content is crafted by seasoned professionals with extensive experience in digital marketing, ensuring you receive accurate and actionable advice.
- Unbiased Information:We provide impartial insights and recommendations based solely on what's best for your business, without any hidden agendas or promotions.
- Thorough Research:Our articles are backed by comprehensive research and the latest industry trends, ensuring you stay informed with reliable and up-to-date information.
- Transparency and Honesty:We believe in complete transparency. We disclose our sources, methodologies, and any potential conflicts of interest, so you can trust the integrity of our content.
- Continuous Improvement:We constantly review and update our content to reflect the latest developments in digital marketing, so you always have access to the most current and relevant information.

The digital era has brought immense benefits to individuals and businesses, but it has also given rise to new threats, one of which is ransomware. With this malicious software on the rise and ransomware gangs becoming more sophisticated, it’s crucial to understand why ransomware is dangerous and take preventive measures.
In this blog post, we will delve into the perils of ransomware, unravel its anatomy, explore its types, and unveil the modus operandi of ransomware gangs. Additionally, we will examine the connection between ransomware and remote access, as well as discuss essential prevention and mitigation strategies to protect against this ever-evolving threat.
Short Summary
- Ransomware attacks pose serious financial and operational risks, with potential ransom demands of up to $70 million.
- Understanding the stages of a ransomware attack is essential for successful prevention strategies, including infiltration methods, encryption process and extortion tactics.
- Prevention measures such as antivirus software, regular backups and user education should be implemented to reduce the risk of ransomware attacks.
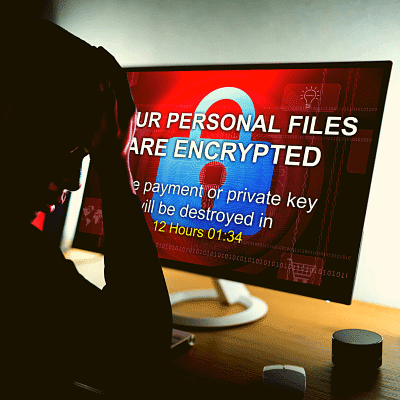
The Dangers of Ransomware Attacks

Ransomware attacks are a serious threat that can have devastating consequences for individuals and organizations alike. The impact of these attacks goes beyond the financial losses, which can range from hundreds of thousands to millions of dollars. Data breaches can occur if the ransom is paid, as attackers may not decrypt files or may steal data.
Moreover, business disruptions are common, with some companies having to shut down operations for days or weeks. With ransomware attackers constantly evolving their tactics, it is vital to stay informed and take appropriate preventive measures to minimize the risks and damage caused by these attacks.
Financial impact
The financial impact of ransomware attacks can be staggering. Direct and indirect costs can include loss of revenue, reputational harm, and even investor confidence. For instance, healthcare organizations may face financial losses associated with revenue loss, remediation costs, brand damage, and legal fees due to ransomware attacks.
In 2021, financial services organizations reported losses over $2 million from ransomware attacks, with ransom demands ranging from $10,000 to millions of dollars, the highest demand being $70 million. These alarming figures underscore the importance of being proactive in protecting against ransomware attacks.
Data breaches
Data breaches are another potential consequence of ransomware attacks. When ransomware encrypts essential files, it can result in the loss of customer data or confidential corporate information. Paying the ransom may not guarantee the recovery of encrypted files and may even lead to further data breaches if the attackers decide to steal or withhold the decryption key.
The victim is left in a precarious position, as the sensitive data in the files cannot be decrypted without a mathematical key known only by the attacker, and the victim must send an untraceable Bitcoin payment to the attacker to regain access. This highlights the importance of preventive measures to protect against ransomware attacks and data breaches.
Business disruptions
Ransomware attacks can also lead to significant business disruptions. In some cases, organizations have to suspend their operations for extended periods of time. This downtime can cause a ripple effect throughout the company, leading to lost productivity, customer dissatisfaction, and damaged reputation.
If customers become aware of a breach of their personal information, they may choose to discontinue using the services of the affected business. The potential long-term effects of a ransomware attack make it essential for organizations to understand the risks and implement effective prevention and mitigation strategies.
Anatomy of a Ransomware Attack
A ransomware attack is not a simple, straightforward process. It involves several stages, including infiltration methods, the encryption process, and extortion tactics. Attackers employ various techniques to gain access to systems, such as phishing emails, malicious websites, and exploit kits.
Once the ransomware has infiltrated a system, the encryption process begins rendering files inaccessible until a ransom is paid. Finally, extortion tactics come into play, with attackers threatening to delete files or publish stolen data if the ransom is not paid.
Understanding the anatomy of a ransomware attack is crucial for developing effective prevention and mitigation strategies.
Infiltration methods
Attackers use a variety of infiltration methods to gain access to systems and deploy ransomware. One of the most prevalent methods is phishing spam with malicious attachments sent via email to the target. Unsuspecting users may click on these attachments, inadvertently infecting their systems with ransomware.
Malicious websites are another common infiltration method, with attackers using these sites to deliver malicious code to the victim’s computer. Additionally, exploit kits are employed to take advantage of security vulnerabilities and infect computers without the need for user deception.
Being aware of these infiltration methods can help organizations and individuals better protect themselves against ransomware attacks.
Encryption Process

The encryption process, which is used to encrypt files, is a crucial component of a ransomware attack. During this stage, the attacker encrypts the victim’s files, making them inaccessible. The files cannot be decrypted without a mathematical key known only by the attacker, and the victim is usually required to send an untraceable Bitcoin payment to the attacker in order to regain access to their files.
Unfortunately, even after paying the ransom, there is no guarantee that the attacker will provide the decryption key or that the files will be decrypted successfully. This emphasizes the importance of taking preventive measures to avoid falling victim to ransomware attacks.
Extortion tactics
Exortion tactics play a significant role in ransomware attacks. Attackers may threaten to delete the encrypted files or publish stolen data if the ransom is not paid. In some cases, ransomware gangs resort to double extortion, where they not only encrypt the data but also threaten to make it public or put it up for sale if the ransom is not paid.
These tactics put immense pressure on victims to pay the ransom, as the consequences of not doing so can be severe. However, paying the ransom does not guarantee a positive outcome, and it is crucial for organizations and individuals to implement effective prevention and mitigation strategies to protect against ransomware attacks.
Types of Ransomware: Locker vs. Crypto
Ransomware can be broadly categorized into two primary types: locker ransomware and crypto ransomware. Locker ransomware restricts access to the user’s system or specific files, while crypto ransomware encrypts the user’s files and demands a payment for decryption.
Within each category, there are further distinctions and variations, making it essential to stay informed about the different types of ransomware and their specific characteristics. Examples of ransomware include Locky, WannaCry, Bad Rabbit, KeRanger, Findzip, MacRansom, and ThiefQuest.
By understanding the different types of ransomware, organizations and individuals can better protect themselves against these threats.
Locker ransomware
Locker ransomware is a type of malicious software that restricts user access to their device, essentially locking them out. Unlike crypto ransomware, which encrypts files, locker ransomware prevents users from accessing their devices or specific files until a ransom is paid.
While this type of ransomware can cause significant disruptions and inconvenience, it is essential to remember that paying the ransom does not guarantee the restoration of access. In fact, it may encourage the attackers and fund their criminal activities.
Therefore, it is crucial to implement preventive measures and have a robust backup plan in place to minimize the impact of locker ransomware attacks.
Crypto ransomware
Crypto ransomware is a more insidious type of ransomware program that encrypts files stored on a computer or mobile device and demands a ransom for the decryption key. It is commonly disseminated through phishing emails or disguised as legitimate software, making it harder to detect. The intent of crypto ransomware is to encrypt important data without disrupting basic computer functions, making it more challenging for victims to identify and address the threat.
Examples of crypto ransomware include Locky, WannaCry, Bad Rabbit, KeRanger, Findzip, MacRansom, and ThiefQuest. Understanding the characteristics of crypto ransomware and staying up-to-date on the latest threats can help organizations and individuals better protect themselves against these attacks.
How Ransomware Gangs Operate
Ransomware gangs, often comprised of ransomware criminals, are highly organized and sophisticated, employing various tactics to achieve their goals. Their operations consist of recruiting and collaborating with other criminals, selecting targets, and using evasion techniques within the targeted operating system.
These gangs often recruit personnel with specific expertise, such as coding, malware development, and network infiltration. They also form strategic partnerships to share resources, including malware code, attack tactics, and payment processing.
Target selection involves identifying susceptible organizations and individuals, while evasion techniques are employed to avoid detection and analysis. Understanding how ransomware gangs operate can provide valuable insights into the nature of the threat and inform the development of effective prevention and mitigation strategies.
Recruitment and collaboration
Recruitment and collaboration are essential aspects of ransomware gang operations. These gangs recruit personnel with particular expertise, such as coding, malware development, and network infiltration. They also form strategic partnerships with other ransomware gangs to share resources, including malware code, attack tactics, and payment processing.
By pooling their resources, ransomware gangs can increase the effectiveness of their operations and maximize their profits. This collaboration highlights the importance of staying informed about ransomware threats and implementing robust prevention and mitigation strategies to protect against these well-organized and sophisticated attackers.
Target selection
Target selection is a critical element of ransomware gang operations, often involving targeted attacks. These gangs select targets based on their susceptibility to attack and the potential financial gains that can be realized. Organizations such as universities, medical facilities, and law firms are often targeted due to their valuable data and potential for financial gain.
Inadequate security protocols and weak supply chains can render organizations more susceptible to ransomware attacks, making them attractive targets for ransomware gangs. By understanding the factors that influence target selection, organizations can take appropriate measures to protect themselves against ransomware attacks.
Evasion techniques
Evasion techniques are an integral part of ransomware gang operations. These techniques help the gangs avoid detection and analysis by security systems. Some common evasion techniques include trusted application abuse, obfuscation, and defense evasion.
Trusted application abuse involves hiding malicious code within legitimate software. Obfuscation makes it difficult to interpret and analyze malicious code, hindering detection efforts. Defense evasion involves circumventing detection by security systems through the use of sophisticated encryption algorithms and multiple layers of encryption.
By understanding these evasion techniques, organizations can better protect themselves against ransomware attacks and develop more effective security measures.
Ransomware and Remote Access

Ransomware and remote access are closely related, as attackers often exploit vulnerabilities in remote desktop protocol (RDP) and virtual private networks (VPNs) to gain access to systems and deploy ransomware. With the increasing reliance on remote work and remote access technologies, it is essential for organizations to be aware of these vulnerabilities and take appropriate measures to protect against ransomware attacks.
By understanding the connection between ransomware and remote access, organizations can implement more effective security measures and minimize the risk of ransomware infection.
Remote desktop protocol (RDP)
Remote Desktop Protocol (RDP) is a proprietary protocol developed by Microsoft that allows users to access and control a computer over a network from a remote location. While RDP can provide significant benefits in terms of productivity and flexibility, it can also be exploited by attackers to gain unauthorized access to systems.
Attackers can exploit RDP vulnerabilities through methods such as brute force attacks, infecting systems with malware, or exploiting weaknesses in the protocol itself. To protect against RDP exploitation, it is essential to use strong passwords, enable two-factor authentication, and maintain regular patching and updating of the system.
VPN vulnerabilities
Virtual private networks (VPNs) are another potential entry point for ransomware attackers. VPNs provide secure remote access to networks, but can be vulnerable to attack if not properly configured and maintained. Ransomware gangs have been known to target vulnerabilities in VPN appliances and protocols, as well as other initial access vulnerabilities, such as unsecured RDP endpoints and email phishing.
Some known exploited vulnerabilities include CVE-2018-13374 and CVE-2020-0796. To safeguard against VPN vulnerabilities, organizations should implement robust security measures, such as using up-to-date VPN software, patching vulnerabilities, and educating users on the potential risks and best practices for VPN usage.
Prevention and Mitigation Strategies
Prevention and mitigation strategies are essential for protecting against ransomware attacks. Implementing antivirus software, conducting regular backups, and providing user education can significantly reduce the risk of ransomware infection. By being proactive and staying informed about the latest ransomware threats, organizations and individuals can minimize the potential damage caused by these attacks and ensure the security of their data and systems.
In the following sections, we will discuss each of these prevention and mitigation strategies in more detail.
Antivirus software
Antivirus software is a critical component of any cybersecurity strategy, as it can detect, prevent, and eliminate ransomware software from computer systems. Some antivirus software that can help protect against ransomware includes Bitdefender Antivirus Plus, AVG Antivirus, Avast Antivirus, Kaspersky, and Malwarebytes Premium. These programs can detect and remove ransomware by scanning for malicious code and blocking malicious websites.
However, it is essential to remember that antivirus software may not protect against all types of ransomware, as some variants may be able to circumvent detection. Therefore, it is crucial to employ a multi-layered security approach and stay informed about the latest ransomware threats.
Regular backups
Regular backups are an essential preventive measure against ransomware attacks, as they can help restore files without having to pay the ransom. The 3-2-1 backup rule recommends maintaining three copies of data, stored on two distinct types of media, with one of the copies located offsite or offline.
By having backups stored in multiple locations, users can ensure that they can recover their files in the event of a ransomware attack. Regular review and updating of backup policies are also crucial to ensure their accuracy and effectiveness.
User Education
User education is a critical aspect of ransomware prevention, as it helps users understand the risks associated with ransomware and the steps they can take to protect themselves. Users should be vigilant against phishing emails and malicious downloads, and be aware of the indicators of a ransomware attack.
Employee cybersecurity education is also essential for organizations, ensuring that employees are aware of potential risks and adhere to best practices in regards to cybersecurity. Implementing user education through training, resources such as videos, articles, and webinars, and regular updates on security patches can significantly reduce the risk of ransomware infection.
Summary
In conclusion, ransomware is a significant and evolving threat that can have severe financial, data, and business impacts. Understanding the anatomy of ransomware attacks, the various types of ransomware, and the operations of ransomware gangs can help organizations and individuals better protect themselves against these threats. By implementing robust prevention and mitigation strategies, such as antivirus software, regular backups, and user education, it is possible to reduce the risk of ransomware infection and minimize the potential damage caused by these attacks. Stay vigilant, stay informed, and stay protected.
Frequently Asked Questions
Can ransomware be dangerous?
Yes, ransomware can be dangerous and cause costly disruptions to operations as well as the loss of critical information and data. Victims may also face legal penalties if their data breach is a result of weak defenses or not complying with cybersecurity laws and regulations.
Therefore, it is important to take proactive steps to protect yourself from ransomware.
Why is ransomware the most damaging type of malware?
Ransomware is the most damaging type of malware because it not only renders data and systems unusable, but also demands a ransom payment in exchange for restoring access. Victims face the difficult decision of paying the ransom or losing access to their data forever.
This malicious software can cause significant disruptions for both individuals and businesses.
What happens if you get ransomware?
If you get ransomware, your data and files could be held hostage. The attacker will likely demand a ransom payment to restore access and decrypt the data.
It’s important to act quickly and contact your IT security team immediately in order to minimize the risk of long-term damage.
What is the difference between locker ransomware and crypto ransomware?
The main difference between locker ransomware and crypto ransomware is that the former restricts access to the user’s system or files, while the latter encrypts data and requires payment for unlocking it.
How do ransomware gangs select their targets?
Ransomware gangs carefully assess potential targets by evaluating the likelihood of a successful attack and the value of potential rewards. By doing so, they are able to select targets that will provide maximum returns for minimal effort.
This process of careful selection helps to ensure that the gangs are able to maximize their profits while minimizing their risk. It also helps to ensure that the targets are chosen carefully and that the attacks are successful.







2 Comments
Excellent article with practical advice for end users. Thank you.
Thanks Alice, glad you enjoyed it!????